Tom Scott explains this in his YouTube video:
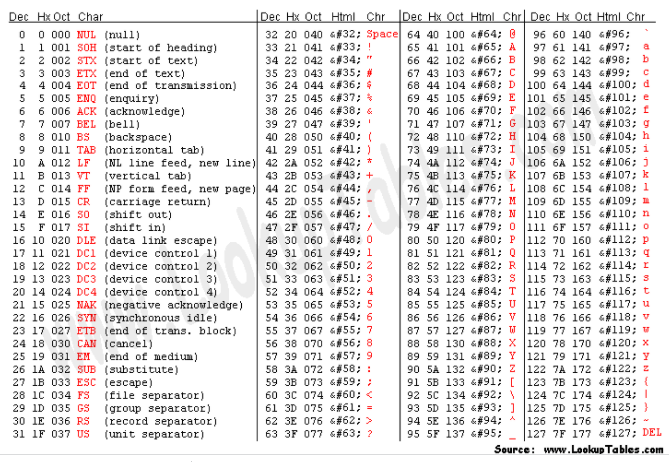
http://a/%%30%30is decoded ashttp://a/%00because%30is0http://a/%00is then further decoded by another piece of code ashttp://a/<NULL>because%00is the NULL character
The bug was originally demonstrated by Andris Atteka who simply added a null character to the string.
Related Posts:
- When you use ‘badidea’ or ‘thisisunsafe’ to bypass a Chrome certificate/HSTS error, does it only apply for the current site? [closed]
- When you use ‘badidea’ or ‘thisisunsafe’ to bypass a Chrome certificate/HSTS error, does it only apply for the current site? [closed]
- When you use ‘badidea’ or ‘thisisunsafe’ to bypass a Chrome certificate/HSTS error, does it only apply for the current site?
- Error `sec_error_revoked_certificate` when viewed in Firefox only
- How do I authenticate WP users from a chrome extension?
- What’s the best approach for generating a new API key?
- Simplest two-way encryption using PHP
- what is a auth_user_file.txt?
- Is moving wp-config outside the web root really beneficial?
- Best way to eliminate xmlrpc.php?
- What’s the easiest way to stop WP from ever logging me out
- If a hacker changed the blog_charset to UTF-7 does that make WordPress vulnerable to further attacks?
- Prevent access or auto-delete readme.html, license.txt, wp-config-sample.php
- What’s the difference between esc_* functions?
- How to set up fail2ban with WordFence?
- Which KSES should be used and when?
- How to remove “Connection Information” requirement on localhost install of WP on MACOSX
- Disable comment windows for all existing posts (pages/blogposts)
- WordPress “Site Health Status” trust it or myself for its security advice?
- Generate WordPress salt
- Stop wordpress automatically escaping $_POST data
- Is WP vulnerable when updating plugins or themes?
- how can i embed wordpress backend in iframe
- Garbage in beginning of wp-config.php – was this WP installation compromised?
- Handling nonces for actions from guests to logged-in users
- Can I force a password change?
- What is the relationship between cURL, WordPress and cacert.pem?
- Is it necessary to use esc_url with template tags such as get_permalink?
- What is pclzip.lib.php file that wordfence think it’s a malicious code
- How to prevent bot or someone to modify any file automatically?
- How to disable XML-RPC from Linux command-line in a total way?
- HTTP Security Headers in wp-config
- How to remove javascript malware in wordpress site [closed]
- Staging Site: Made Public – Security Questions
- Best Way to Enable Two Step Authentication
- Securing my WordPress Files and Directories
- Single sign-on: wp_authenticate_user vs wp_authenticate
- How to allow internal links using wp_kses filtration
- Securing a multi-user permission structure
- How does Cross Site Scripting (XSS) work exactly? [closed]
- Is default functions like update_post_meta safe to use user inputs?
- No option “I would like my site to be private, visible only to users I choose” in Privacy Settings
- How does the “authentication unique keys and salts” feature work?
- vs WordPress Security
- esc_html__ security : what for in this example?
- Securing wp-config leads to sensitive information leak on wp-settings
- Suspicious Files
- What’s the point of forbidding access to wp-config.php?
- wp-json and what data does it give away?
- Is is necessary to use security plugin for wordpress? [closed]
- neccessary?
- wp-config.php being written by attacker
- XML-RPC errors they know my username?
- Is [admin / admin] acceptable for all local websites?
- Simple Online Payment for Event Registration [closed]
- Client side HTTP parameter pollution (reflected)
- Local file inclusion critical security issue [closed]
- my wordpress website is suspended [closed]
- Malware script in database post table only? [closed]
- Best practices to assert current_user_can() with guests
- XMLRPC slow and weird websites/services
- iTheme Security always lockout my account [closed]
- Is it sensible to worry about sanitizing admin input in plugin custom CSS?
- WordPress Front end Form – Enable to Submit PHP Codes
- Is it safe to hand over the admin rights?
- Is it safe use wp_editor in public contact form
- Is WordPress MultiSite secure & how much can it scale? [closed]
- How safe is current_user_can()?
- Is it safe to give wordpress directories ownership to www-data?
- How can I force a specific password?
- Do we need to escape data that we receive from theme options?
- Why does WordPress change a file’s permissions?
- Side effects of disallowing *.php requests in production environment?
- Outgoing new connection to linked Websites – why?
- My Site keeps crashing due to the wp-confg file being deleted
- Someone keeps changing my SITEURL (mysql injection or xss?) [closed]
- Who updates the wp-admin/core file?
- Replace domain in database
- Does this code indicate an exploit?
- What highest security brake with wordpress and static files?
- Spam in WordPress root folder
- Has anyone developed a anti-spam plugin to simply allow users to BLOCK whatever they wish to, but one that will also go easy on IP addresses?
- how to protect wordpress content from crawler
- Can WordPress admin user + database credentials be used to gain Cpanel or FTP access?
- Should I worry about SQL injection when using REST API?
- Links to root domain from search engines don’t work, but direct links and links from other referrers do
- How can I backup my site if it gets hacked?
- Cannot access wp admin of WordPress website (security plugin issue) [closed]
- Why are the latest visits to my website originating from my own website?
- How do I hide WordPress users from security scanning?
- Background Updates Not Happening
- wp-config.php file and code injection
- FORCE_SSL_ADMIN affecting subdomains
- What is the best security $_POST method?
- Is WordPress ready for GDPR compliance? [closed]
- Should WordPress Add Options to Enhance Security or Leave it to plugin developers? [closed]
- Move data from wp-config to another file
- Heartbleed: What is it and what are options to mitigate it?
- OpenVPN vs. IPsec – Pros and cons, what to use?
- How to test if my server is vulnerable to the ShellShock bug?
